When we share data In SharePoint with a user outside our directory, SharePoint will by default use a one-time code sent to the user so the user can verify their identity.
This is also the case with OneDrive and if you do it from teams using open in SharePoint.
But let us see this in action.
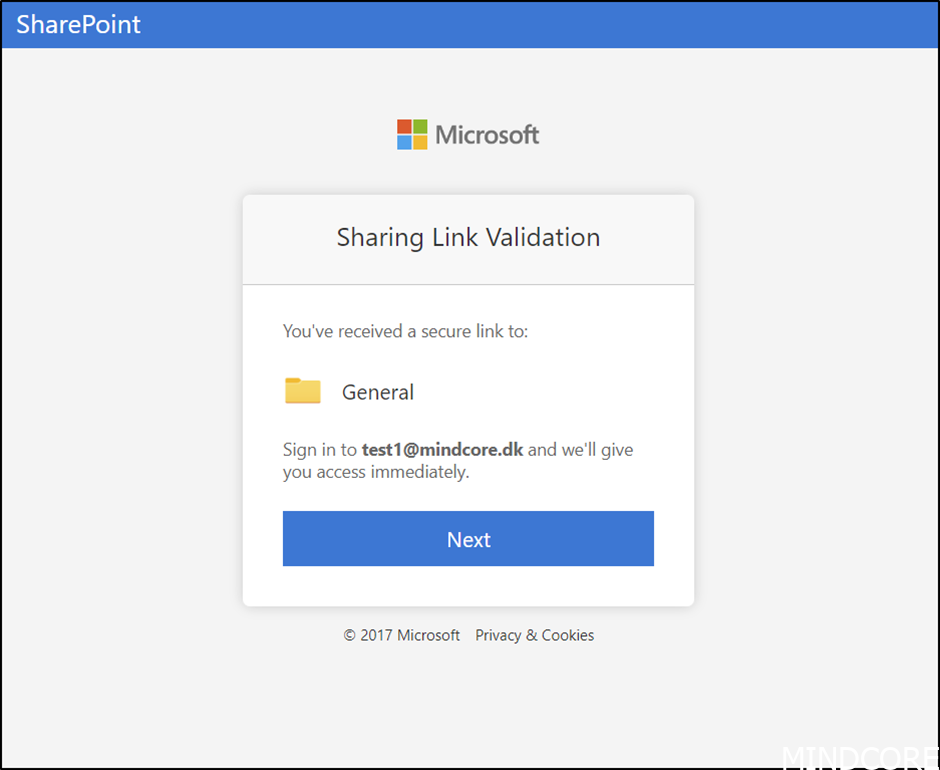
As the guest user you will receive a mail informing you of what is shared and a link to the shared content.
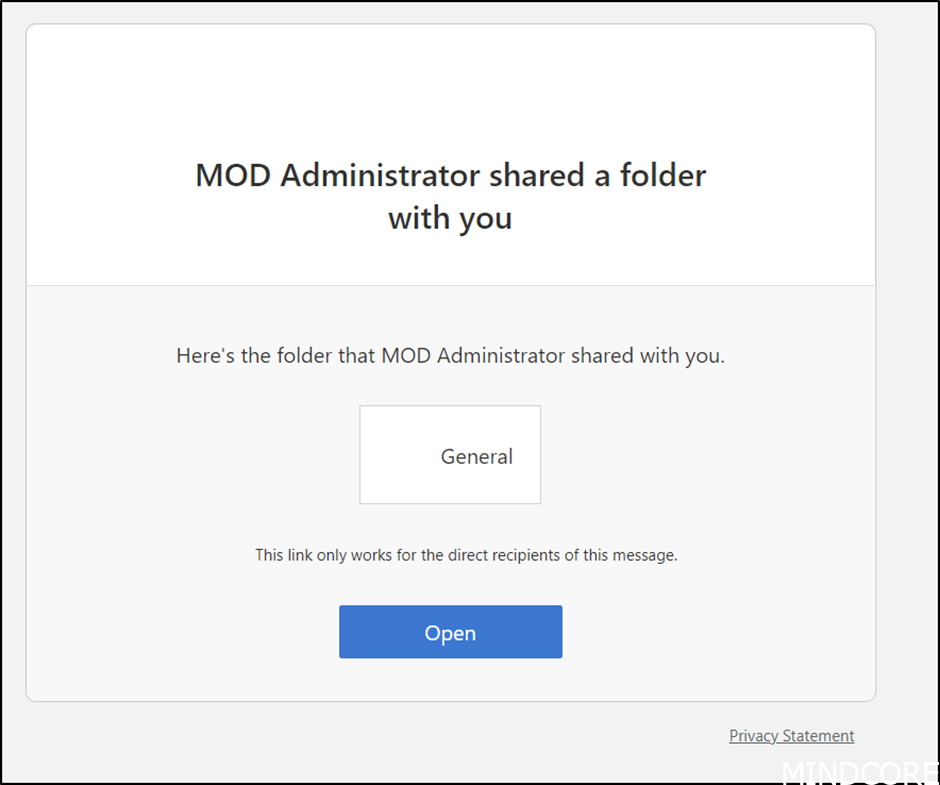
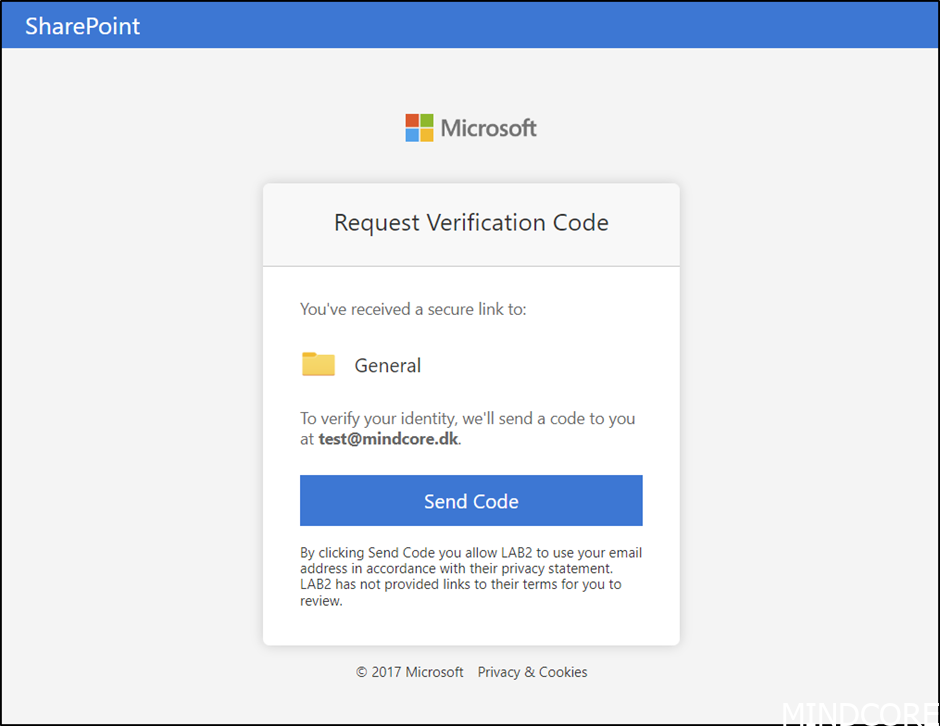
If we open the link, we can get a verification code send by mail.
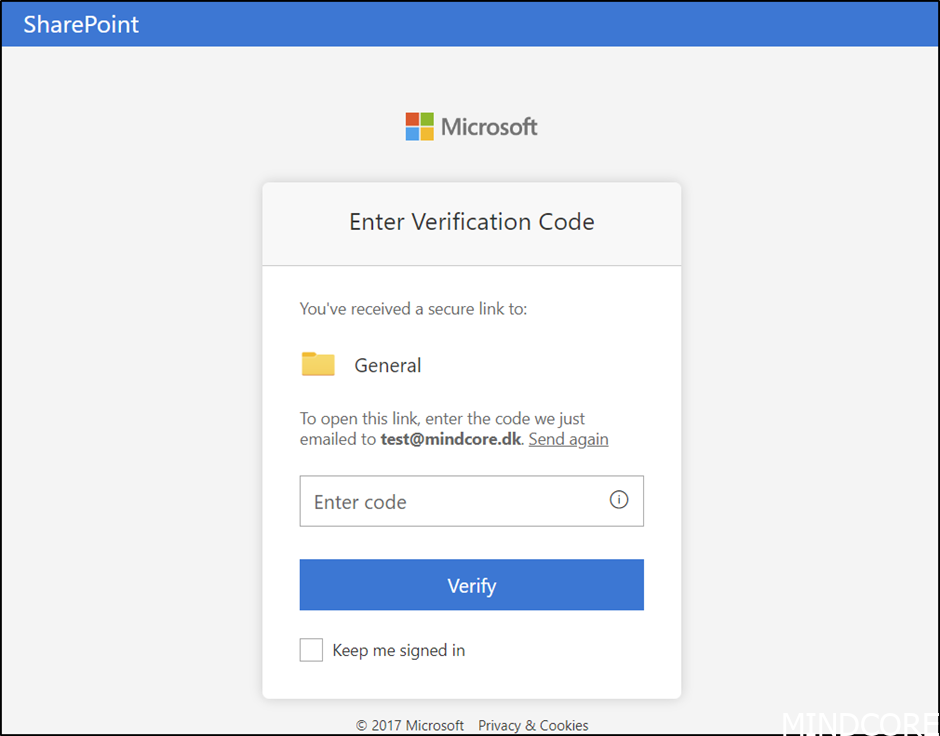
And when we enter the code received, we get access.
If we look in SharePoint, we can now see the added user.
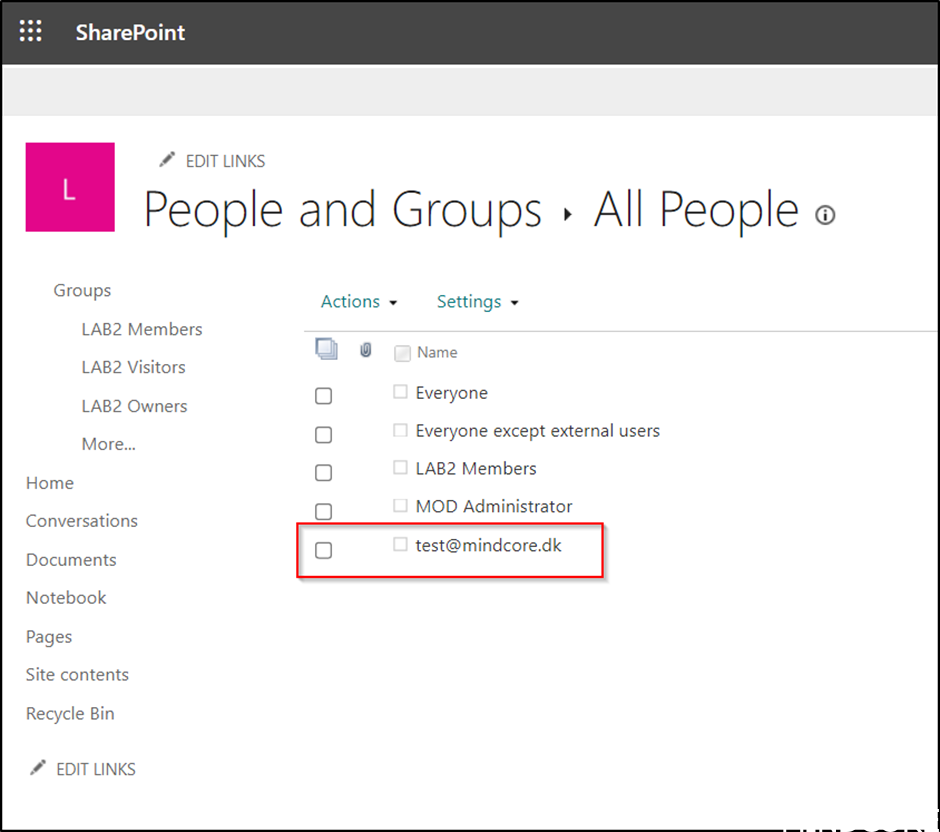
To see all users, we add GroupId=0 to the site as shown here.
_layouts/15/people.aspx?MembershipGroupId=0
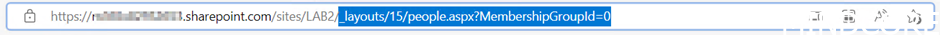
And if we click on the user, we get this information.
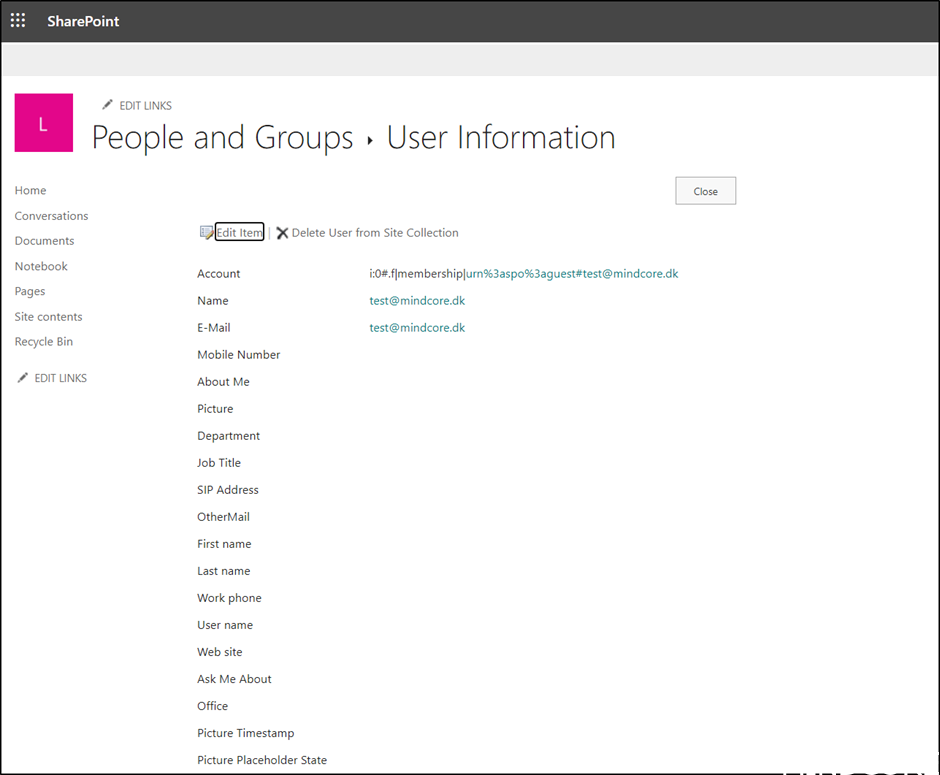
If we look in Azure AD no guests are created.
So, the user is only created in SharePoint, but for guest governance this is not the best approach.
Instead, we would want to integrate SharePoint with Azure AD.
Azure AD provides much better authentication and management of guests.
Authentication still happens with a one-time passcode when they do not already have a work account or a Microsoft account.
Once the integration is enabled, we do not need to reshare or migrate guests.
If someone outside our organization clicks on a link that was created before Azure AD integration was enabled, SharePoint will automatically create a new Azure AD guest account.
Unfortunately, this integration is currently not enabled by default, but we strongly recommend to enable it 😊
But let us do a test drive of this integration.
You can find the setup documented here Link
And a bit more on the traditional “Ad hoc” sharing here Link
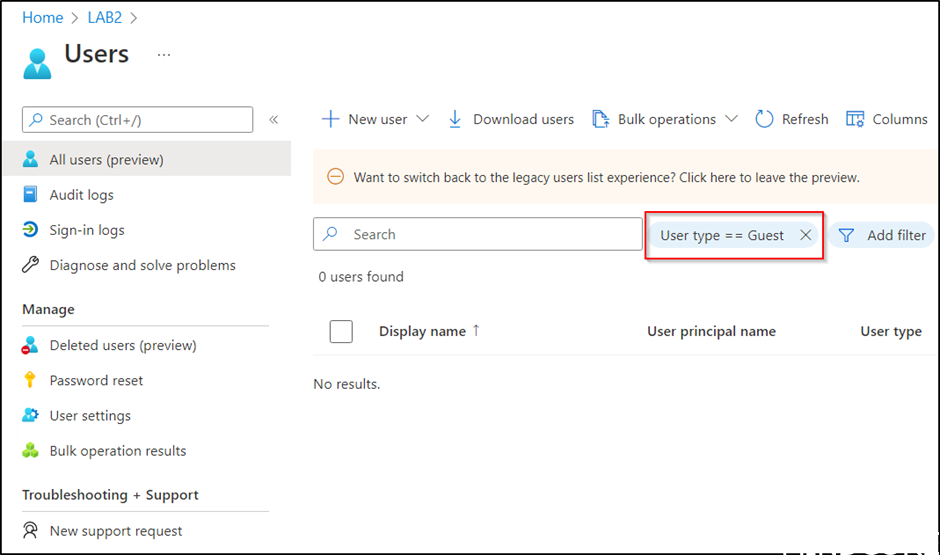
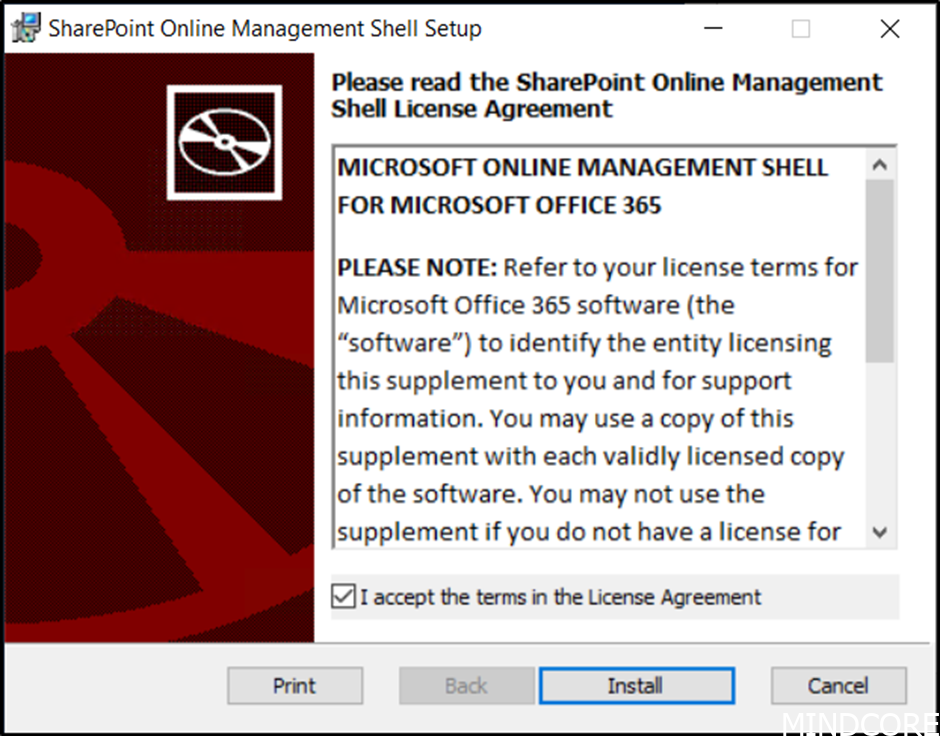
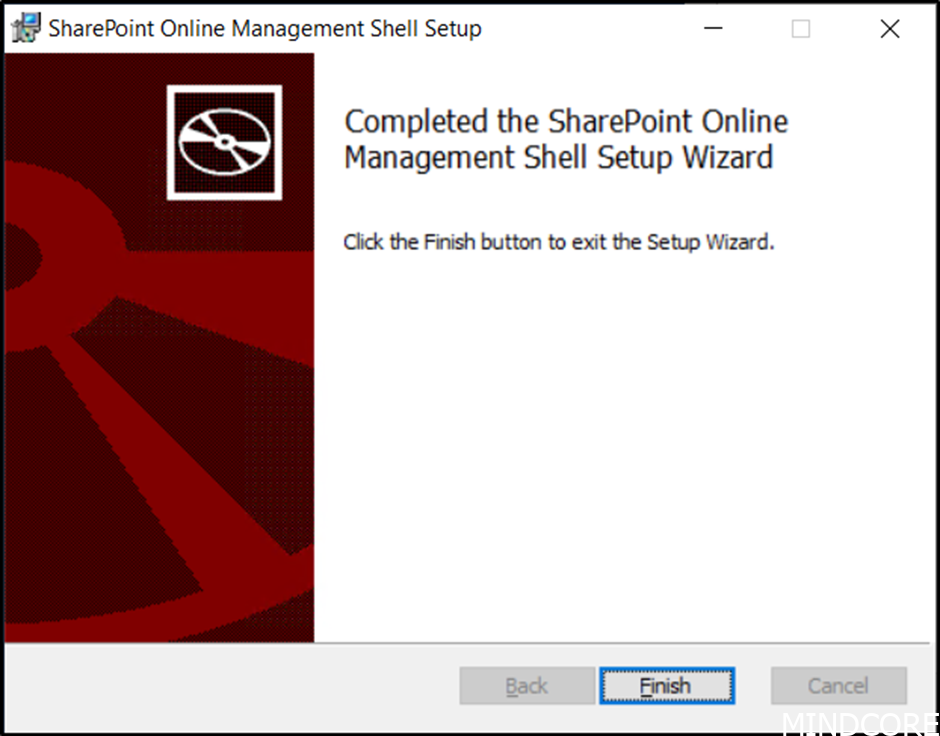
First, download the SharePoint Online management Shell Download
And install it.
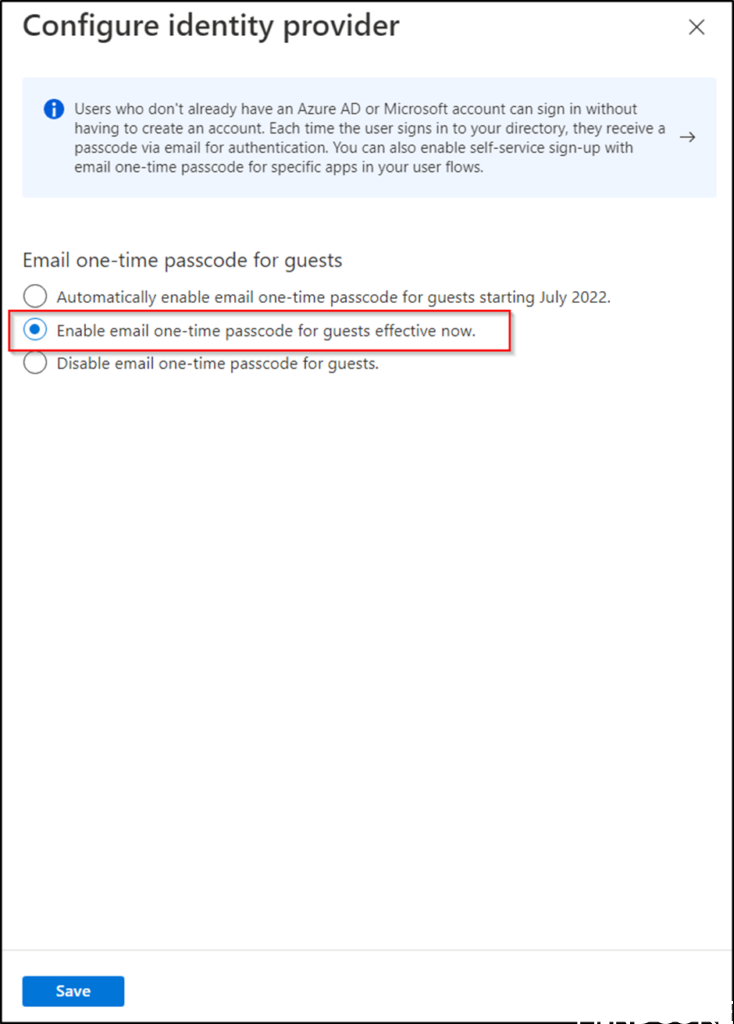
Next, we need to enable email one-time passcode for guests, go to the Azure AD portal and navigate to External identities.
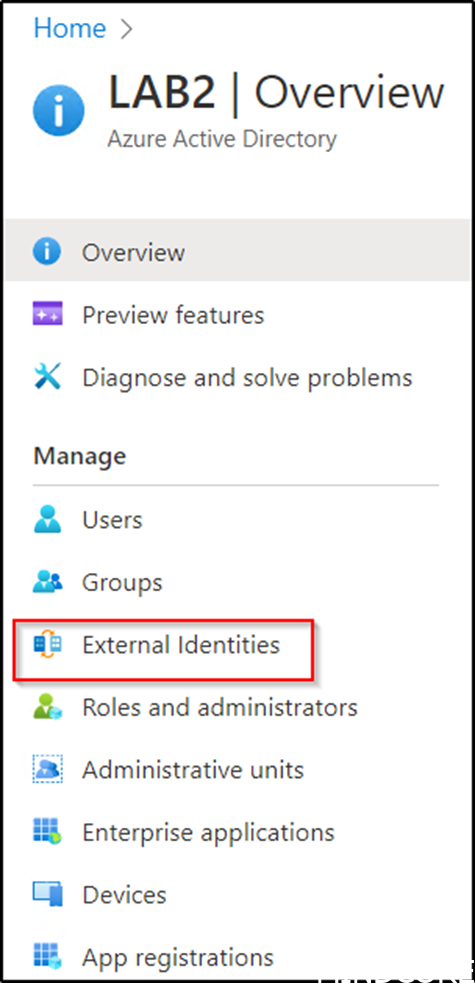
Then All identity providers and Email one-time passcode.
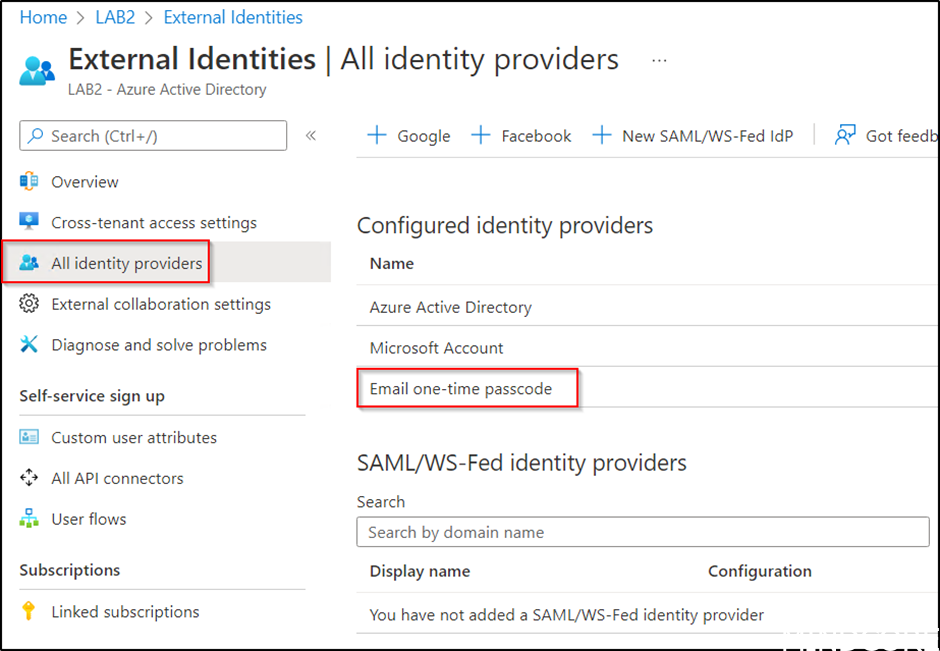
Then enable Enable email one-time passcode for guests effective now and save.
Using PowerShell connect to SharePoint as a global admin or SharePoint admin and verify status with the command:
get-SPOTenant | select *B2B*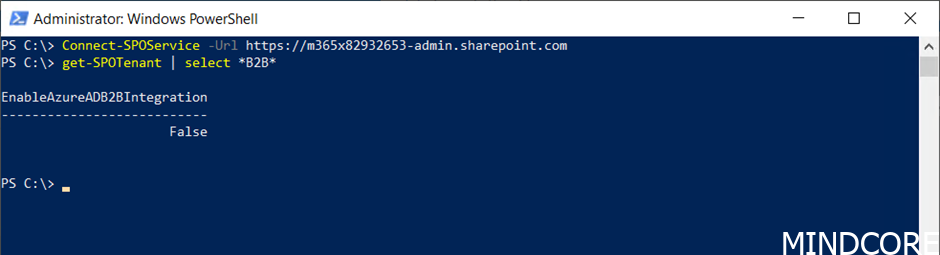
And if not enabled as we expect, then enable the integration with the following commands:
Set-SPOTenant -EnableAzureADB2BIntegration $true
Set-SPOTenant -SyncAadB2BManagementPolicy $true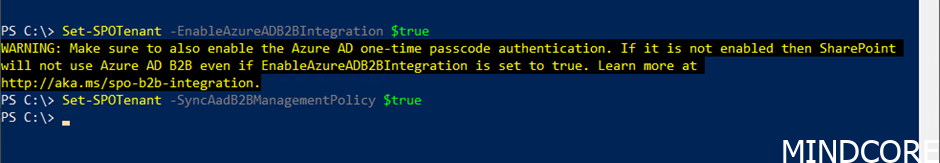
Verify change with the command:
get-SPOTenant | select *B2B*
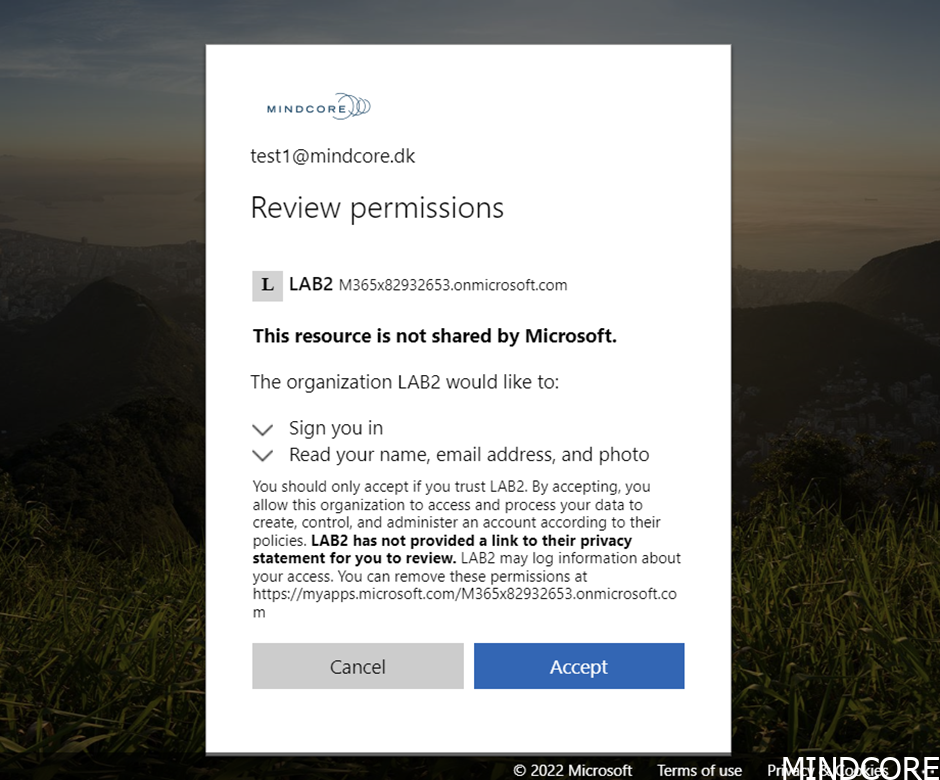
If we now invite a guest, you will immediately see the change in the dialog presented for the guest.
The user will now have to accept the permissions required from the tenant.
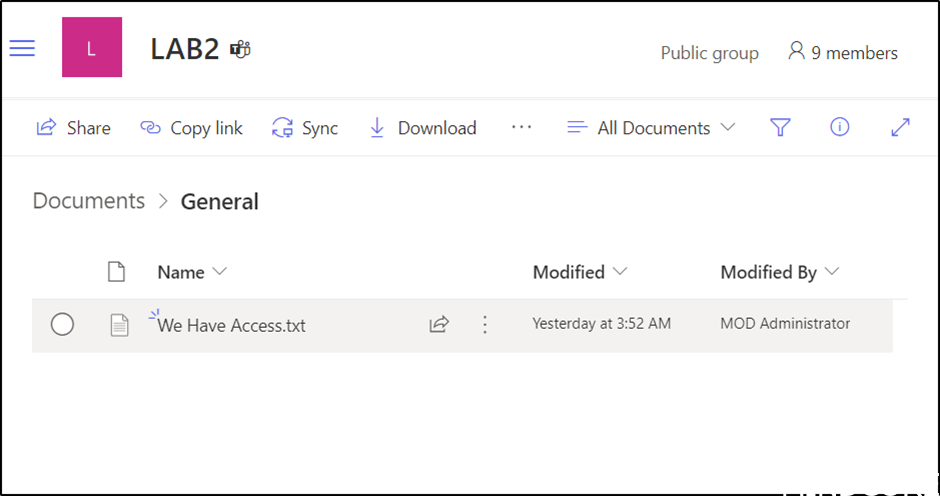
And we have access.
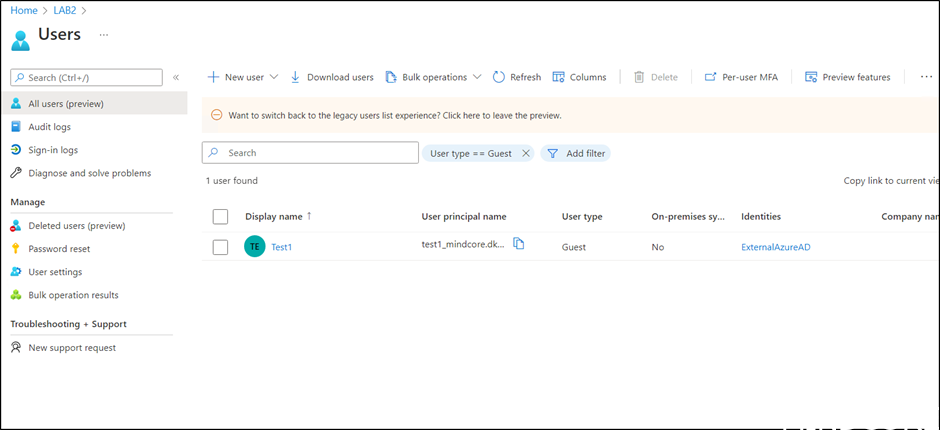
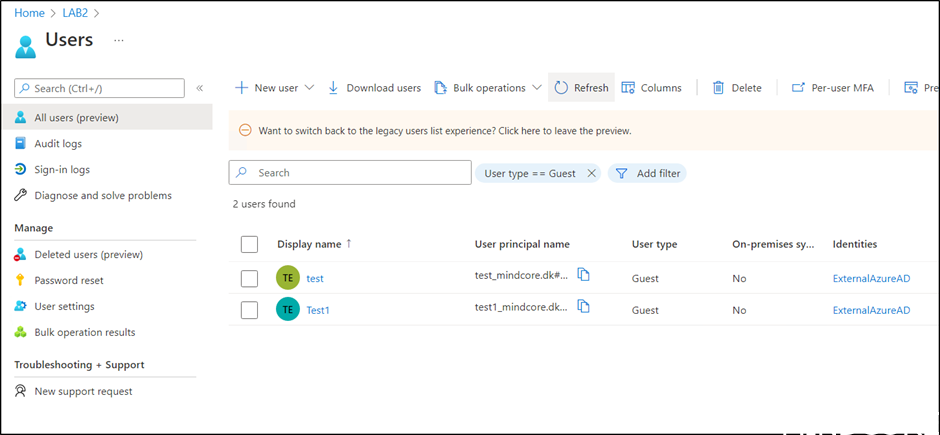
If we now look in Azure AD a Guest is created.
If we try with the original guest user, we also need to accept permissions required from the tenant.
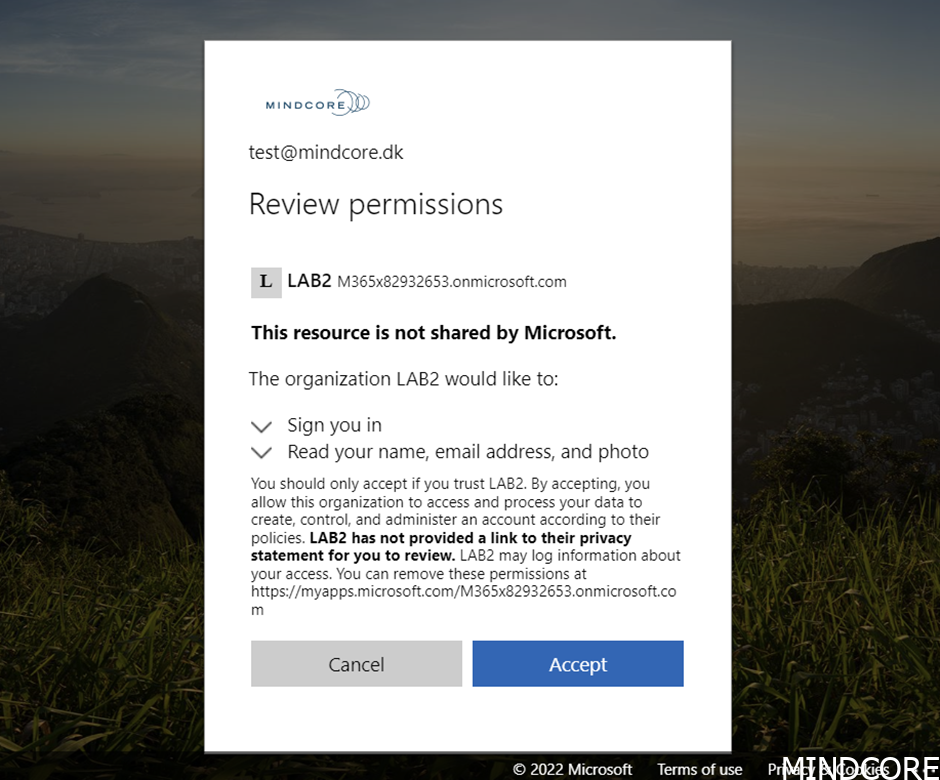
And our original guest is now also in Azure AD.
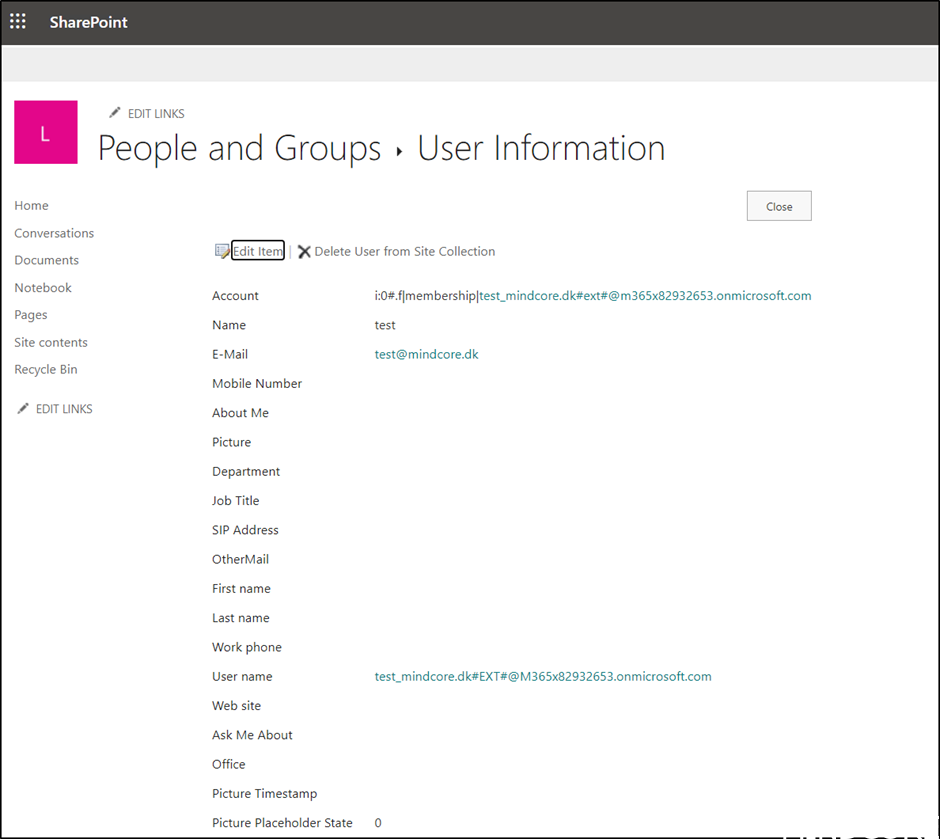
If we take a closer look at the original user in SharePoint (using &Force=True trick to bypass Delve😊)
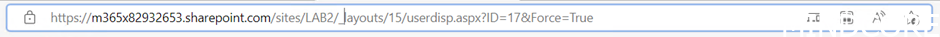
We can see that the Account and User Name now shows that the User is an Azure AD guest.
Using Azure AD for guests allow us to use conditional Access and Access Reviews, which is some of the most important impacts of this change.
Happy testing 😊












