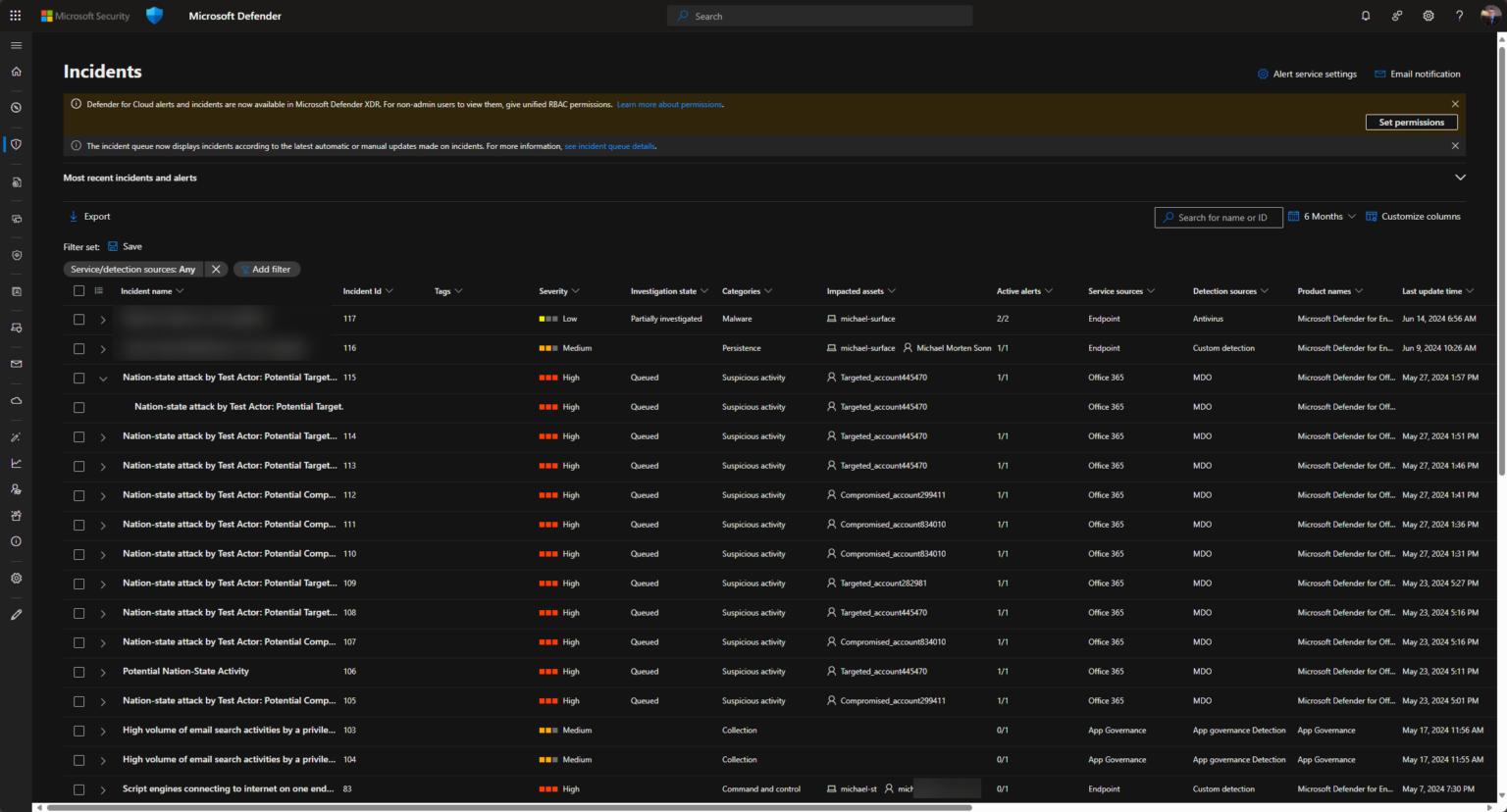
Microsoft Defender – Nation State Notifications
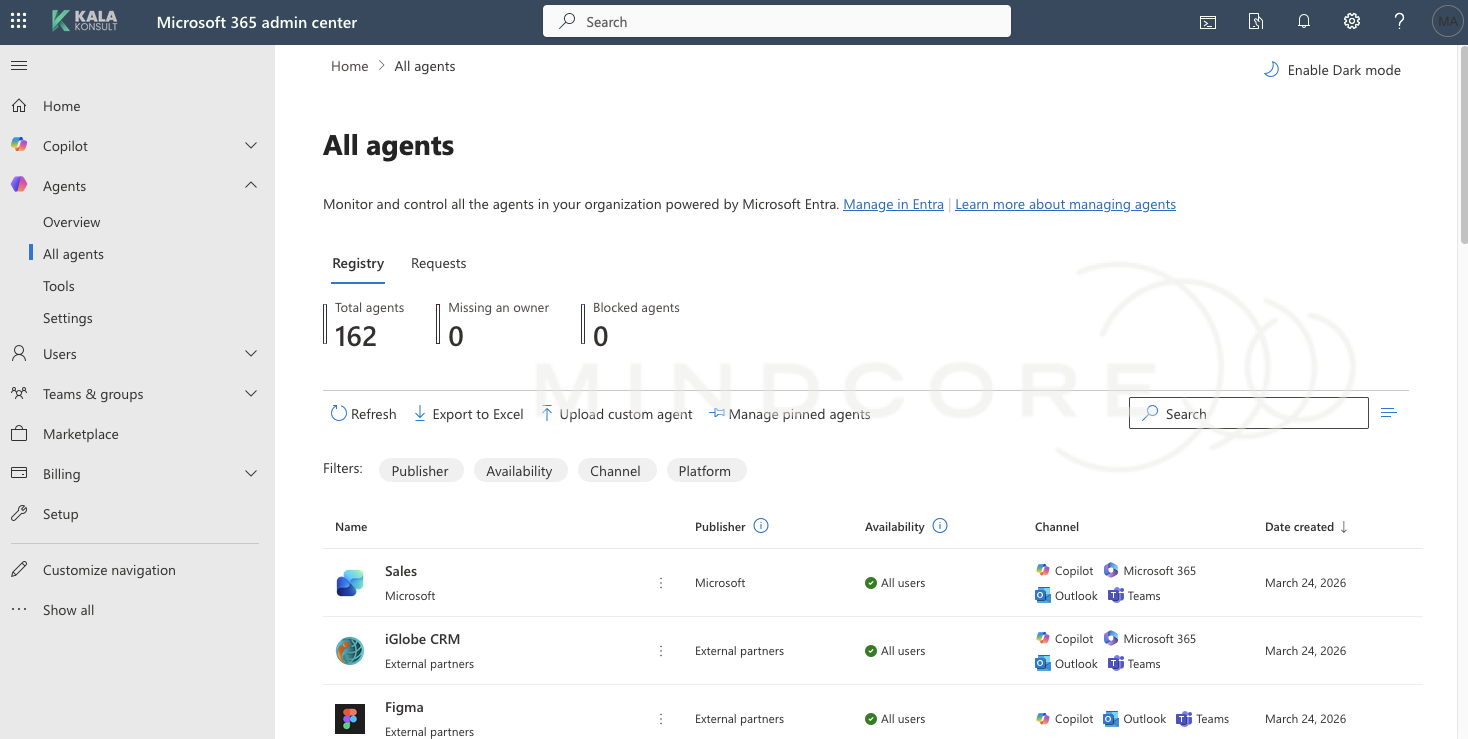
Introduction To safeguarding customers against evolving cybersecurity threats is a top priority for many vendors. As part of Microsoft´s ongoing commitment to security excellence, they introduced a new initiative aimed last year to bolstering your organization’s defenses: nation-state activity alerts! What is Nation-State Activity Alerts Nation-state activities represent some of the