When we use Windows Hello for Business and a user forgets the PIN, it can be reset directly from the sign-in page.

By default, this will be a destructive PIN reset, the existing PIN, and underlying credentials, including any keys or certificates added to their Windows Hello container, will be deleted from the client and a new log in key and PIN provisioned.
Note that for hybrid Azure AD-joined devices, users must have corporate network connectivity to domain controllers to complete destructive PIN reset. This is also a good reason why the non-destructive reset is better.
But let us try a default destructive PIN reset.
We can view the current PIN reset configuration using this command
dsregcmd /statusIf CanReset has status DestructiveOnly, then only destructive PIN reset is enabled, just as we expected in this case.

Before we do the reset, we can check the current certificate dates with this command.
certutil -csp "Microsoft Passport Key Storage Provider" -key -v
Or by simply looking at the certificate in the user store.
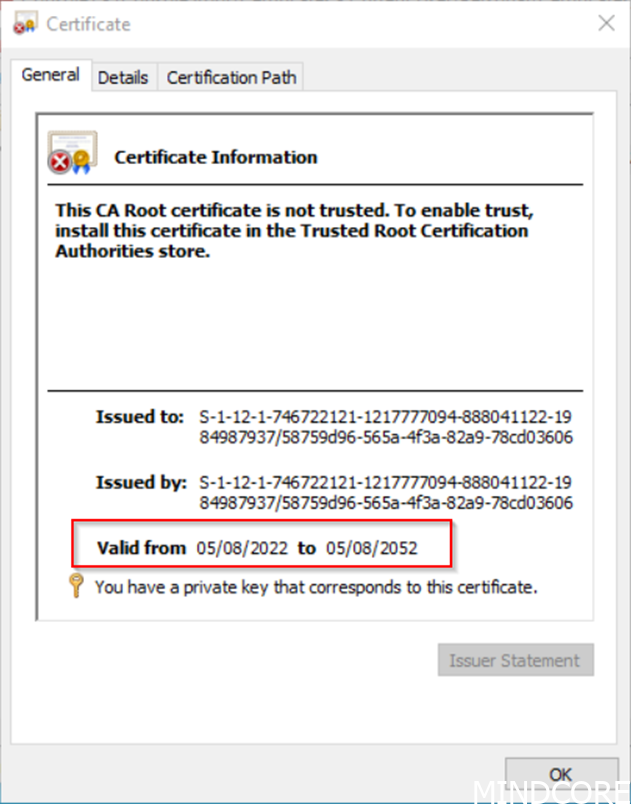
These dates should change when we do a destructive reset because a new certificate is issued.
After requesting a PIN reset from the login screen, we will need to enter the user password.

We need to respond in the authenticator app.

Now notice the warning, if you reset your PIN, apps might require you to sign in again, and any data that’s managed by an organization could be lost. This warning is showed because this is a destructive PIN reset.

Then we can enter a new PIN, again notice that the text says Set up a PIN, again because this is a destructive PIN reset.

All is done.

We can now sign in with the new PIN, and we have done a destructive PIN reset.
If we now look at the certificate, we can see that it is indeed a destructive reset, because date has changed.

Now let us setup non-destructive reset and try again.
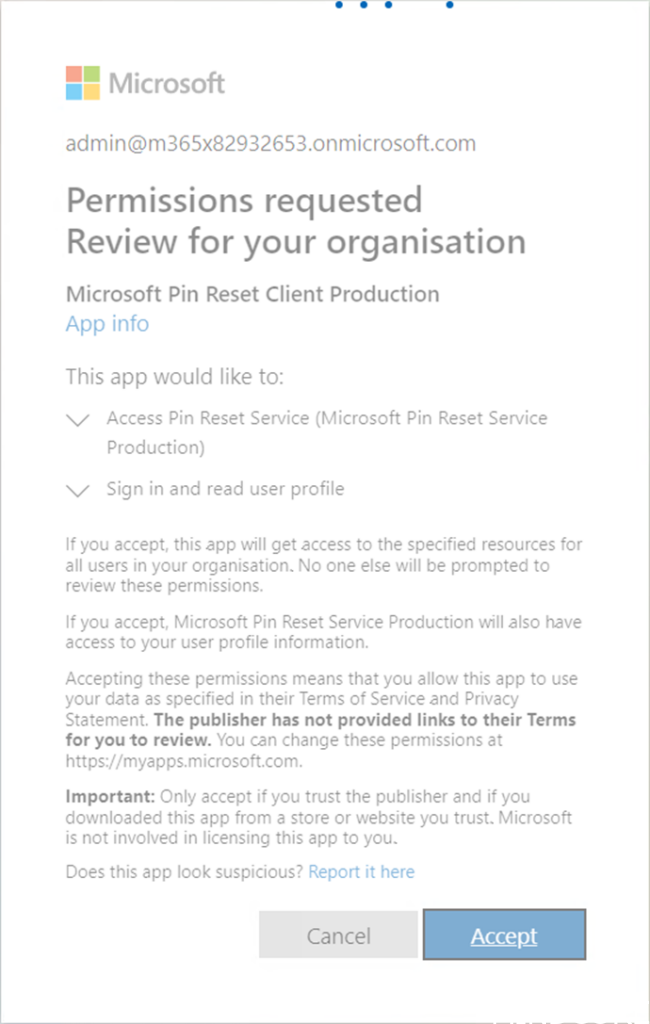
We need to approve the following app Permissions using a Global Administrator account, go to this link first Microsoft PIN Reset Service Production website

When you click Accept you will see the following information.

Next approve the following app Permissions using a Global Administrator account, go to this link Microsoft PIN Reset Client Production website

This time you will not get a good response (at least when I tested), for me it just responded like this and never timed out, but I did the job, we will check this manually in next step.
In Azure AD go to Enterprise Applications, and filter on the word PIN, you should see both Microsoft Pin Reset Service Production and Microsoft Pin Reset Client Production in the list, then we are ready to continue.

Before we can test the non-destructive PIN reset, our devices must be configured to enable PIN Recovery, this can be done with the Settings Catalog as shown with red.

You can also use the Endpoint security blade and an Account protection Policy as an alternative.

When the client has updated its settings we can again use the command.
dsregcmd /statusIf CanReset has status DestructiveAndNonDestructive, then non-destructive PIN reset is enabled., just as we expected in this case.

Now let us test and do a PIN reset, but again we will first check the current certificate.

We will do the reset just like we did with the destructive reset, so I will only show you the screenshots with another dialog.
We will get no warning.

And it will be a PIN change not a new setup.

Now if we again look at the certificate nothing has changed after the reset.


It is very easy to setup non-destructive PIN reset, so I recommend that you also enable this.
For more information go to the documentation here Link and this Hello for Business FAQ
Until next time happy testing 😊













